
Overall rating:
4.4/5
Good
Sharevault
Free trial: Yes
Ease of use
Average 4.1
Customer Support
Average 3.9
Ease of setup
Average 4.2
Global rankings
Sharevault virtual data room software:
the complete guide
ShareVault data room is an on-demand web application with bank-grade security and rich functionality. The solution enables secure document sharing during due diligence and other vital business processes. Commonly, ShareVault is used in life sciences, financial and legal services, private equity, investment banking, energy, legal, and venture capital.
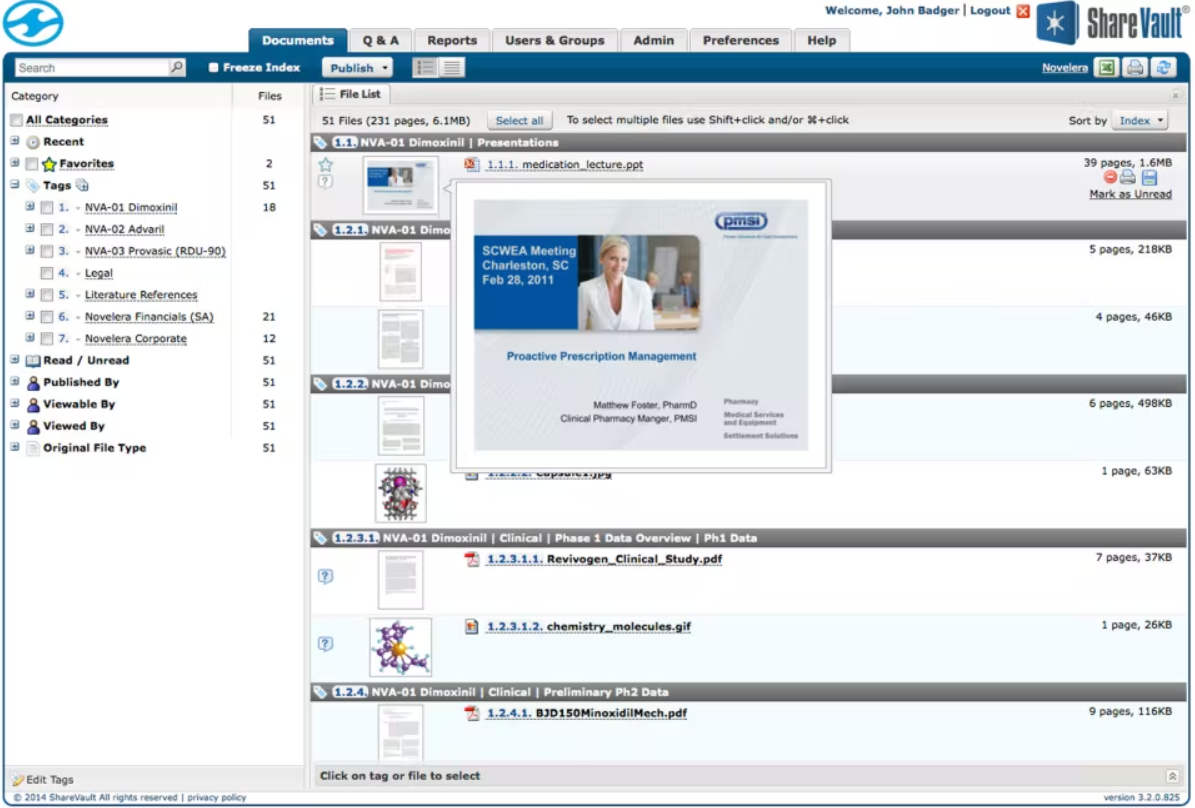
Software screenshots
Security features
Being a certified ISO/IEC 27001:2022 provider, ShareVault implements robust measures to protect its security management systems, ensuring data integrity and confidentiality. It respects user privacy and complies with GDPR and CCPA standards, self-certifying for the E.U.–U.S., U.K.–U.S., and Swiss–U.S. Privacy Shield frameworks.
Admins can set up a ShareVault account in 33+ geographic regions within Amazon Web Services’s (AWS) global infrastructure. The user experience is seamless across these regions, requiring just one password and profile for a smooth login process.
ShareVault security features for document security include the following:
- Remote shredding. Virtual data room admins can revoke a user’s access to a document even after downloading it. It ensures that sensitive information is secure and removed from unauthorized access.
- Dynamic watermarking. Dynamic watermarking applies identifiable marks to sensitive documents, associating them with specific users. This feature discourages unauthorized sharing or distribution of the content.
- Granular access controls. The software allows setting up security policies on a per-user, per-group, and per-folder basis. This customization ensures that only authorized individuals can access highly confidential documents.
- Secure printing. This tool prevents users from printing PDF documents — even when printing is allowed. It helps companies protect sensitive materials from unauthorized reproduction.
- Expiration date. ShareVault users can set specific deadlines for document access by establishing an expiration date and time. After this period, documents can no longer be opened.
Sharevault data room features
Security
User and data management
Customization
Pricing
ShareVault offers three pricing plans. Express best suits users who upgrade from budget data rooms or generic file-sharing platforms. The Pro plan is ideal for projects requiring extensive functionality and premium technical support. Lastly, its Enterprise plan best meets the strict audit and compliance needs of large organizations.
The provider does not publicly share pricing. Potential customers can request it through the official website. Additionally, ShareVault offers a free 7-day trial with unlimited usage and 24/7 support.
Top 3 data rooms software
Overall rating:
4.9/5
Excellent

Overall rating:
4.8/5
Excellent
Overall rating:
4.7/5
Excellent
Unique features
Here are some distinctive tools that the ShareVault platform offers:
- Secure audio/video player. The player allows secure playback of A/V files directly in a browser. Users upload media, and ShareVault automatically transcodes it for high-quality playback, supporting various file formats like MP4 and AVI. With built-in rights management and optional dynamic watermarking, all content remains protected.
- Batch print. When printing is allowed, users can choose several documents, click the batch print button, and generate a personalized booklet with a table of contents, page numbers, and separator pages.
- Inter-document hyperlinking. This feature resolves the issue of broken links when uploading documents. ShareVault automatically scans for links to other files and replaces them with the correct ShareVault URLs. It allows users with the right permissions to click and instantly access related documents.
- Zoomable thumbnails. Zoomable thumbnails provide a quick glimpse of the first page of each document. Displayed alongside every document, these miniature images allow users to hover over them for an instant zoomed-in view within virtual data rooms.
Customer support
The provider offers proactive and knowledgeable service throughout a project. Furthermore, its experts assist users during the data room setup, configuration, and deployment.
Customer support features include the following:
- Dedicated project manager. Expert managers provide personalized advice on effectively utilizing ShareVault for specific applications.
- 24/7/365 telephone hotline. Virtual data room administrators and end users can always access technical support to keep projects on track.
- Comprehensive training. New customers receive personalized training sessions with a ShareVault expert. These sessions optimize the learning experience to help users understand the platform’s features.
- Migration services. The provider assists with the migration from other data rooms or file-sharing systems to ShareVault software.
- Remote screen sharing. Support specialists use remote screen-sharing software to address issues quickly.
Document management
ShareVault virtual data rooms make managing multiple documents and files easier and more organized. Here are its most unique, advanced features:
- Secure batch download. ShareVault allows users to download multiple encrypted documents simultaneously for added security and the ability to remote shred.
- Index auto-numbering. When reordering or adding new items, the numbering updates automatically. Thus, all business documents stay organized and up-to-date.
- Instant full-text search. Users can search their entire ShareVault instantly, with results ranked by relevance. The powerful search engine also supports features like keyword stemming (e.g., searching “finance” will include “financials” and “financing”) and international character sets.
- Favorites. Users can mark specific files or tags as favorites for quick access. A simple filter shows only the favorite items, making navigation faster.
- Drag-and-drop reordering. This data room tool simplifies content organization, allowing users to reorder files and tags without losing track of their original structure. The system automatically updates numbering and controls the data structure as items are rearranged.
While the feature set of ShareVault virtual data rooms may seem robust, understanding user experiences provides valuable context and highlights how the tools perform in real-world scenarios. So, next, we explore user feedback to see how ShareVault works in practice.
Pros and cons
Speaking of Sharevault’s particular benefits, users most often report its intuitive search feature. Thanks to it, documents can be found easily, using the filter and keyword functions that turn in your results in a matter of seconds, hence helping to save considerable time. Sharevault also allows users special branding features that allow you to customize your data room in your brand colors and add your logo.
The user interface is intuitive and simple to use despite its high-end design. And best of all, users can access Sharevault’s 24-hour support service anytime it’s required.
- Assistance with onboarding
- Screen capturing and text copying blocking
- External file sharing with security controls
- Practical user activity and document engagement reports
- Helpful whitepapers and learning materials
- Creation of document index at no cost
- Steep learning curve
- Tedious file uploads due to manual tagging
- Unpredictable pricing structure based on MB used
- No unique features compared to other vendors
Clientele and case studies
Here are some of ShareVault’s leading clients categorized by industry:
- Life sciences: AlloCure, Aragon, LG, Eisai, and Human Genome Sciences
- Energy: Piramal, BP, Terrestrial energy, Tetra, and Nucsafe
- Private equity: Verod, Versa, Westmoore, Hidden River, and TRC
- Investment banking: Corewest Capital, Ceres, and M&S Fairway
- Legal: Jones Day, Howard & Howard, LPMA, and Squire Sanders
Potential customers can also discover how ShareVault customers use the software by watching the videos on its website.
Comparison of the top 3 data rooms
 |  | ||
| Details | Check price | Learn more | Learn more |
| General business | |||
| Top use cases | M&A, Finance, Life sciences and healthcare, Energy, Real estate, Tech | M&A, Finance, Legal | M&A, IPO, Capital raising, Healthcare, Real estate |
| What users appreciate | Excellent support, easy-to-use, encryption and security features | Encryption, data analysis tool, support | Reliable support, comfortable platform |
| Features | |||
| Fence view | |||
| Granular access permissions | 8 levels | 4 levels | 5 levels |
| Dynamic watermarking | |||
| Built-in redaction | |||
| Two-factor authentication | |||
| Advanced Q&A | |||
| Automatic reports subscription | |||
| Detailed audit trail | |||
| Auto-notifications about new activity | |||
| Custom branding | |||
| Support | |||
| Live chat | |||
| Email support | |||
| Phone support | |||
FAQs
What is Sharevault?
ShareVault is a virtual data room for securely sharing sensitive documents with corporate workers and outside parties. It features document management, activity tracking, and data protection tools. This platform is used by large, medium, and small businesses, venture capitalists, investment bankers, and law firms for expedited due diligence.
Is Sharevault secure?
ShareVault data room is a secure data-sharing platform for information-intensive business deals. It is deployed in a Virtual Private Cloud and hosted by Amazon Web Services. Also, the solution includes a two-step verification, 256-bit data encryption, and customer-managed keys.
How much does Sharevault cost?
Sharevault cost is unavailable on the official website. However, the provider presents three tariff plans, such as Express (a budget data room), Pro (for projects requiring extensive functionality), and Enterprise (for enterprise-wide deployment).
What services does Sharevault provide?
ShareVault provides simple and secure data-sharing tools complemented by granular user access controls, fast data search, and access from any device. Additionally, ShareVault customers can rely on comprehensive 24/7 support and a dedicated project manager to resolve all their questions or issues quickly and efficiently.